David Barzilai, chairman and co-founder of automotive cyber-security firm, Karamba Security, has applauded the UK government for taking pre-emptive action and zeroing in on preventing cyber-attacks as critical for the adoption of self-driving cars on a mass scale. However, he says the guidelines don’t go far enough toward effectively preventing car hacking, saying cars are not servers or mobile phones that can sustain the risk of hidden security bugs. The time it takes to remediate such bugs in production,
August 8, 2017
Read time: 3 mins
David Barzilai, chairman and co-founder of automotive cyber-security firm, 8519 Karamba Security, has applauded the UK government for taking pre-emptive action and zeroing in on preventing cyber-attacks as critical for the adoption of self-driving cars on a mass scale.
However, he says the guidelines don’t go far enough toward effectively preventing car hacking, saying cars are not servers or mobile phones that can sustain the risk of hidden security bugs. The time it takes to remediate such bugs in production, while hackers exploit them and create damage, can compromise consumers’ safety.
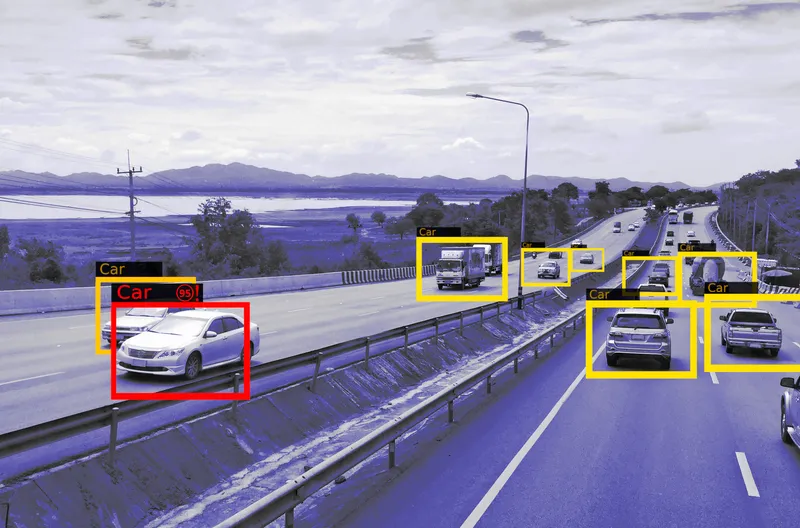
Smart vehicles are increasingly becoming the norm on British roads, allowing drivers to access maps, travel information and new digital radio services from the driving seat. But while smart cars and vans offer new services for drivers, it is feared would-be hackers could target them to access personal data, steal cars that use keyless entry, or even take control of technology for malicious reasons.
Tough new %$Linker:2 External <?xml version="1.0" encoding="utf-16"?><dictionary /> 0 0 0 oLinkExternal government guidance false http://www.gov.uk/government/publications/principles-of-cyber-security-for-connected-and-automated-vehicles false false %> aims to ensure engineers developing smart vehicles will have to toughen up cyber protections and help design out hacking. The government is also looking at a broader programme of work announced in this year’s Queen’s speech under the landmark Autonomous and Electric Vehicles Bill that aims to create a new framework for self-driving vehicle insurance.
The guidance contains eight principles, setting out how the automotive sector can make sure cyber security is properly considered at every level, from designers and engineers, through to suppliers and senior level executives. These include:
Barzilai says cars enter production with thousands of hidden security bugs. It is unavoidable, as all software has bugs and cars have between 10m to 100m lines of code, in each car. As autonomous cars get more sophisticated and as more human navigation tasks, such as looking around and steering, move to the car, the danger increases. Hackers can hack into a car through its internet-connected features such as the vehicle-to-vehicle (V2V) communications system, and once in, they can work their way into the rest of the car’s controls.
However, he says, cars have a significant cyber-security enabler, which should not be overlooked. Cars should run as they operate in-factory. Any unauthorised change to factory settings must be malware. Hardening the car’s externally-connected controllers according to their factory settings prevents cyber-attacks, when hackers try to exploit security bugs, before hackers succeed to infiltrate the car and without sending frequent security patches to the field.
However, he says the guidelines don’t go far enough toward effectively preventing car hacking, saying cars are not servers or mobile phones that can sustain the risk of hidden security bugs. The time it takes to remediate such bugs in production, while hackers exploit them and create damage, can compromise consumers’ safety.
Smart vehicles are increasingly becoming the norm on British roads, allowing drivers to access maps, travel information and new digital radio services from the driving seat. But while smart cars and vans offer new services for drivers, it is feared would-be hackers could target them to access personal data, steal cars that use keyless entry, or even take control of technology for malicious reasons.
Tough new %$Linker:
The guidance contains eight principles, setting out how the automotive sector can make sure cyber security is properly considered at every level, from designers and engineers, through to suppliers and senior level executives. These include:
- Organisational security is owned, governed and promoted at board level:
- Security risks are assessed and managed appropriately and proportionately, including those specific to the supply chain:
- Organisations need product aftercare and incident response to ensure systems are secure over their lifetime;
- All organisations, including sub-contractors, suppliers and potential 3rd parties, work together to enhance the security of the system;
- Systems are designed using a defence-in-depth approach;
- The security of all software is managed throughout its lifetime;
- The storage and transmission of data is secure and can be controlled;
- The system is designed to be resilient to attacks and respond appropriately when its defences or sensors fail.
Barzilai says cars enter production with thousands of hidden security bugs. It is unavoidable, as all software has bugs and cars have between 10m to 100m lines of code, in each car. As autonomous cars get more sophisticated and as more human navigation tasks, such as looking around and steering, move to the car, the danger increases. Hackers can hack into a car through its internet-connected features such as the vehicle-to-vehicle (V2V) communications system, and once in, they can work their way into the rest of the car’s controls.
However, he says, cars have a significant cyber-security enabler, which should not be overlooked. Cars should run as they operate in-factory. Any unauthorised change to factory settings must be malware. Hardening the car’s externally-connected controllers according to their factory settings prevents cyber-attacks, when hackers try to exploit security bugs, before hackers succeed to infiltrate the car and without sending frequent security patches to the field.