With permission from a local road agency, researchers in from the
The team, led by University of Michigan computer scientist J. Alex Halderman, found three major weaknesses in the traffic light system: unencrypted wireless connections, the use of default usernames and passwords that could be found online and a debugging port that is easy to attack.
“The vulnerabilities we discover in the infrastructure are not a fault of any one device or design choice, but rather show a systemic lack of security consciousness,” the researchers report in a paper they’re presenting this week at a computer security conference. They did not disclose exactly where in Michigan they did the research.
Although the road agency responsible for implementing the system has never faced serious computer security threats, the possibility will become more of a problem as transportation authorities and car makers test new ways for infrastructure and vehicles to communicate in order to reduce congestion and accidents.
“They need to be worrying about this and think about security - it needs to be one of their top priorities,” says Branden Ghena, a graduate student who worked on the project. “It’s hard to get people to care about these things in the same way that it’s hard to get people to change their passwords.”
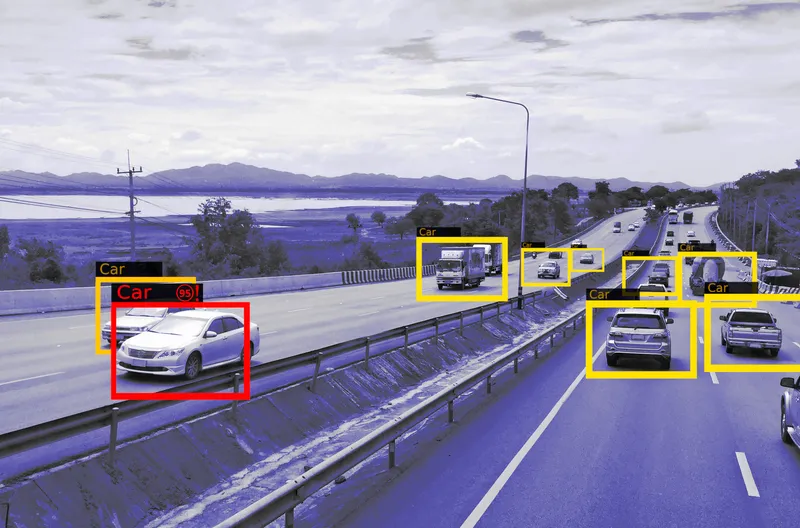
Wirelessly networked traffic lights have four key components. There are sensors that detect cars, controllers that use the sensor data to control the lights at a given intersection, radios for wireless communication among intersections, and malfunction management units (MMUs), which return lights to safe fallback configurations if an ‘invalid’ configuration occurs. For example, if somehow every light at an intersection is green, the system might fall back to having them all become flashing red lights.
The Michigan researchers found that anyone with a computer that can communicate at the same frequency as the intersection radios, in this case, 5.8 gigahertz, could access the entire unencrypted network. It takes just one point of access to get into the whole system.
After gaining access to one of the controllers in their target network, the researchers were able to turn all lights red or alter the timing of neighbouring intersections, for example, to make sure someone hit all green lights on a given route. They could also trigger the lights’ MMUs by attempting invalid configurations.
At the end of their report, Halderman and his group propose simple recommendations for improving the security of traffic infrastructure. First and foremost, traffic-system administrators should not use default usernames and passwords. Also, they should stop broadcasting communications unencrypted for ‘casual observers and curious teenagers’ to see.
The researchers note that their study has implications beyond traffic lights. More and more devices like voting machines, cars, and medical devices are computer controlled and will ultimately be networked. This phase change, as they call it, comes with “potential for catastrophic security failures.”
MIT researchers hack into traffic lights
With permission from a local road agency, researchers in from the University of Michigan hacked into nearly 100 wirelessly networked traffic lights, highlighting security issues that they say are likely to pervade networked traffic infrastructure around the country. More than 40 states currently use such systems to keep traffic flowing as efficiently as possible, helping to reduce emissions and delays.
The team, led by University of Michigan computer scientist J. Alex Halderman, found three major weaknes
August 22, 2014
Read time: 3 mins