By 2019 there will be almost 44 million connected cars globally and by 2022 that figure will be nearer 70 million; some 40% will be electric powered, according to market analyst
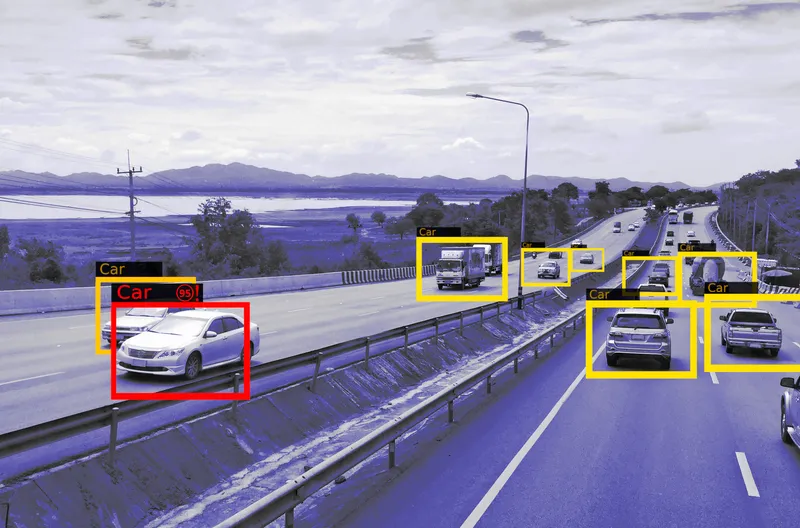
Traditionally, the car has been a secure, closed environment. But connected vehicles (CVs) are potentially open, and thus of interest to the maliciously-minded, with more than 50 points of vulnerability that can be used to threaten people’s lives and automakers’ reputation.
A webinar hosted by Frost and Sullivan’s head of digital transformation, Jean-Noël Georges, discussed the current state of play with Christine Caviglioli (vice-president of automotive of digital security specialist M2M Gemalto) and Yvan Gravier, CEO of French CV open data startup Eliocity.
Cybersecurity management and the building up of consumer confidence will be the two decisive factors for the continued growth of the CV sector, warned Georges. He cited Fiat Chrysler’s voluntary safety recall of some 1.4 million cars and trucks equipped with radios that enable remote updating of the in-vehicle software.
The recall, to check the vehicles’ security against possible imitation attacks by hackers, followed the high-profile cyberjacking of a Cherokee Jeep. Those responsible were able to remotely manipulate some of the vehicle’s critical functions, including transmission, steering and brakes. At that time Fiat Chrysler stated that, to its knowledge, there had not been a real-world incident of remote hacking into any of its vehicles and that the recall had found no defects.
“But,” stressed Georges, “it is now becoming obligatory for auto-industry OEMs to actively pursue cybersecurity measures rather than simply trying to mitigate the risks.” These can include breaking into cloud infrastructures, ‘sniffing’ data from communications networks and intruding into a vehicle’s engine control unit or infotainment system.
“Once these risks are being better planned for, however”, he continued, “the CV revolution will prove to be a fantastic opportunity for the traditional players to reinvent the way in which consumers interact with automakers and their vehicles.” He pointed to the likes of Apple CarPlay and Android Auto, which are already making themselves felt in the connected car market; with Apple nurturing plans to mimic its software role inside the vehicle. “These are providing opportunities for the automotive industry to reinvent itself; but the levels of encryption will be critical.”
Caviglioli highlighted the importance of building a ‘chain of trust’. This has to run from the initial design and the vehicle’s manufacture, to its sale through a dealership and continued via periodic diagnostics and maintenance (while accommodating changes of ownership) to final scrapping. “Security will need to be both by default and design, with the emphasis on protecting what matters, where it matters and when it matters,” she continued, emphasising the need for the protection of the contained data in a car along the way.
The ownership issue, stressed Gravier, will become all the more relevant in an era when people will no longer be using individually-owned cars as all-purpose vehicles, but looking for the optimal mobility solution for each specific need – including the sharing of connected cars. These, he said, will include upgraded, existing vehicles as well as new ones coming fully equipped off the production lines. Aftermarket installation for connectivity will need to be carried out by reliable companies.
There will also need to be clear protocols for the sharing of, and creating value from, the data generated by and collected from connected cars while out on the roads, with implications for its long-term management and security.