As security threats become increasingly vast and varied, multinationals are beginning to see the need for an effective global security operations centre to protect their organisation. James I. Chong spells out what is required
You know you need a global security operations centre (GSOC) to support what you’ve built, identify threats, and prevent disasters before they happen - but how do you know if it’s truly effective? There’s no shortage of information coming into operation centres. Too often, it’s the quality of the data and the inability to correlate it quickly from independent sources that pose the greatest challenges. You need to harness data in real time to make informed decisions that will increase safety, security and efficiency.
GSOCs can empower security operators with a platform that delivers ongoing detection and mitigation of threats to both cyber and physical systems, and it can uncover vulnerable areas, respond to potential threats and address incidents occurring within your organisation’s environment.
So, why doesn’t every company already have a GSOC in place? It’s a common misconception that an advanced operations centre would be a huge, complicated undertaking that wouldn’t fit within a budget. To the contrary, with the appropriate planning and technology, your organisation can lower its risk and increase operational efficiency and situational awareness without exponential costs.
In order to outline what you want the GSOC to achieve for your business, your company should interview its stakeholders about what they expect. The importance of involving everyone from your executives to your IT department depends on your company’s size and purpose of the GSOC. This is where your chief security officer (CSO) can lead the charge in co-ordinating the integration of physical and IT systems in order to create a full picture of your company infrastructure.
Next, assess what the goals of your operations centre will be. For instance, is it to improve loss prevention techniques through monitoring supply chain management and efficiency? Perhaps the main goal is to lower overall company risk by creating better ID management processes or tying together video surveillance from multiple company locations so they can be accessed at any time from anywhere?
Prioritise all of the potential goals among your key stakeholders, with the ultimate aim of increasing collaboration and pre-empting risk.
Here are six steps to creating a customised GSOC for your organisation:
1. Establish goals upfront
An effective GSOC provides full control over the system and dynamic workflow standard operating procedures, easily allowing for changes to be made to rules, devices and maps in near real-time.
In order to maximise the efficacy of a GSOC, you need to listen to your customers, asking those invested what they need and expect. Fill any gaps that you discover. Encourage communication between individual personnel and empower them to speak up. Make sure your procedures evolve alongside the needs of your stakeholders and maintain consistent communication with them
2. Create a customised platform
Enable dynamic geospatial mapping and display of situations, people and alarms for fixed and mobile devices and display location data supporting incidents in real time for each specific situation or even globally across all situations. An effective GSOC analyses and correlates data, events and alarms and identifies ‘true’ and ‘false’ situations so time and money are spent on the most critical incidents first. It proactively highlights potential situations based on rules and standard operating procedures and prioritises incidents.
3. Use your existing infrastructure
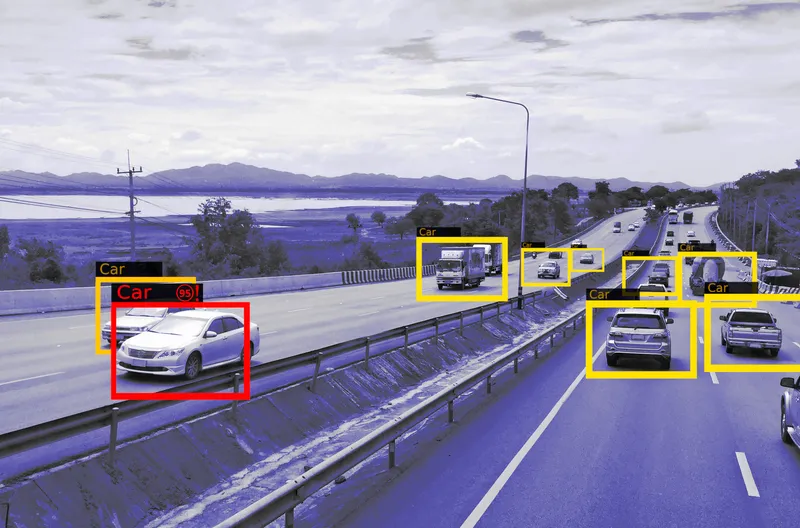
Instead of approaching your GSOC with a ‘rip and replace’ methodology, take your current technology into account and see how you might be able to pull in existing data sources that you may not be fully utilising - sensors, cameras, access points, and any other standard technology platforms that can be of use. By surveying the current environment, you will be able to identify the holes in your security strategy and directly address those first. A converged security approach means combining and leveraging data from all sources within your company - from cameras, sensors, access control, building management, alarms, ID management and even social media - to correlate and extract actionable information that can positively impact your organisation from a security and financial perspective.
4. Improve integration - and communication
Create a truly agnostic, standard and open Physical Security Information Management (PSIM) / Converged Security Information Management (CSIM) / Internet of Things (IoT) platform. Along with third-party systems, develop an architecture that is comprehensive and easily integrates physical security devices, social media, cyber activity and private/public feeds. Ensure you meet ONVIF standards for interoperability and integration requirements to extend integration.
An effective GSOC leverages a diverse connector library with numerous integrations, like alarms, sensors, cameras, identity management, access control and analytics, giving administrators unlimited options for customising. You should also develop partnerships with product solutions that connect with your software, providing an ever-expanding range of solutions.
5. Find the right fit
Finding the right data management and correlation platform is essential to the GSOC. When reviewing different platforms, keep in mind the functions that the GSOC must perform. These include security system administration, compliance, situational awareness capabilities (both within and outside of your organisation), incident management, crisis communications and 24/7 monitoring.
Once you lay out all of your company’s needs, you can begin pricing and identifying which solutions are a priority. If you’re looking to develop an effective GSOC, but are wary of the amount of work that it will take, you should shop to find a solution that works for your specific needs. There are various levels of platforms that can fit your specific needs and will help you connect independent systems and collect and aggregate data on a centralised platform so security leaders can see the complete picture and make informed decisions. Most importantly, you have to consider your organisation’s needs now - and in the long term. Make sure to prioritise your goals based on a forward-thinking plan.
6. Test your approach
Process-driven decision-making is key to the success of your GSOC. Once you’ve defined your goals, accounted for your assets, chosen a platform and allocated appropriate resources, you can give your GSOC the green light. Be sure to train the operators or analysts who will run the platform on an ongoing basis and outline specific processes and procedures at the launch.There are many benefits to having an effective GSOC, including shortened response times, continuous monitoring, detailed analysis and actionable information. Through laying a firm foundation and following through to execution, companies can leverage a GSOC platform to deliver tangible, end-to-end solutions for a variety of applications.
By accelerating innovative physical security platforms along with IT and cybersecurity methods, organisations can gain the analytical insights that are needed to address specific challenges.